Certified Evasion Techniques Professional (CETP) - Review 🚀

Hey again everyone! This is Foued SAIDI: Senior Penetration Tester at Intrinsic-Security , holder of CRTE, CRTP, CARTP and CADPenXv2 professional certifications, Web3/Blockchain Security Researcher and Bug Bounty Hunter.
I have recently passed my Certified Evasion Techniques Professional (CETP) certification from Altered Security and I would like to share my feedback regarding it along with a few tips for anyone planning on passing it.
CETP Overview

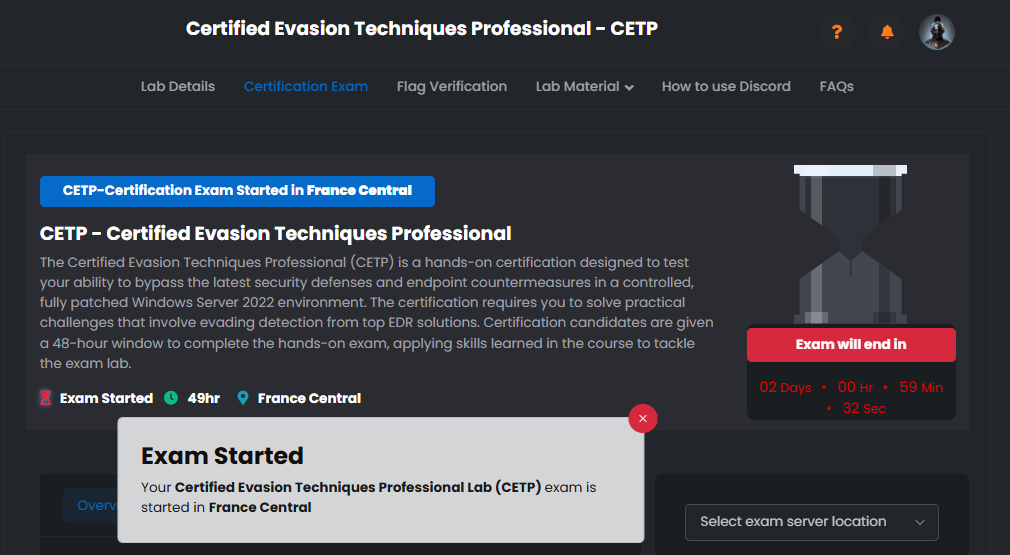
First of all, CETP is a 48-hour certification where the holder has the expertise to evade modern Endpoint Detection and Response (EDR) solutions on a fully-patched Windows Server 2022 infrastructure by purely abusing Windows internals, kernel-level techniques and custom tradecraft.
What I really like about Altered Security is that their professional certifications only rely on real-world techniques and actual offensive research, not some unrealistic stuff. CETP really takes this to a whole other level: you’re going head to head with live EDRs (MDE, Sysmon, and Elastic EDR) and you have to actually understand HOW they work to bypass them.
I consider achieving this certification a really worthwhile investment as it includes lifetime access to the course material, walkthrough videos and Tools alongside one exam attempt. The lab access starts at 449$ for 30 days (60 days at 649$ and 90 days at 849$). In case of failure, the retake fee is also a reasonable 99$ with a 1-month cooldown period. The certification is valid for 3 years with a free renewal exam before expiry (or via CRTM).
Course Content
Regarding the course content, we were provided with access to the new Altered Security platform which is a centralized hub for all your certs and materials: 40+ hours of course videos, learning objectives walkthroughs, full course slides, a lab manual and finally all the necessary Tools and source code which is a HUGE plus.
The course is split into 17 chapters that take you from Windows internals all the way to advanced rootkit and anti-analysis tradecraft:
- Windows Internals
- EDR Internals
- Static Detection Bypass
- Initial Access Techniques
- Introduction to Kernel Development
- Path to Kernel Exploitation
- EDR Neutralization Techniques
- Attacks on Kernel Callbacks
- Attacks on Event Tracing for Windows (ETW)
- PPL & Credential Guard Bypass Techniques
- Advanced Evasion Techniques
- Advanced Rootkit Techniques
- C2 Traffic Tunneling
- Blocking EDR Network Traffic
- Attack Surface Reduction (ASR) Bypass
- Attacks on Sysmon
- Anti-Analysis Techniques
While going through the course, you’ll be learning a LOT of stuff regarding advanced Windows tradecraft and modern EDR evasion: from Windows internals, PE structure analysis, user-mode and kernel-mode components, to reverse engineering EDR solutions to understand how they actually collect telemetry, to custom obfuscation and code virtualization to bypass static detection.
You will be taught almost ALL the techniques there are to actually break modern endpoint protection: kernel programming and exploitation through vulnerable drivers, EDR killing through signed killer drivers, kernel callback removal, ETW patching and provider disabling, PP/PPL bypass to dump LSASS from protected processes, DSE bypass, ASR rules bypass, UAC bypass, signed ClickOnce backdooring for initial access, custom rootkit development and a lot more.
Compared to other evasion courses out there, the CETP took a deeper dive into the actual internals: we didn’t just run tools, we literally reverse engineered EDRs with IDA Pro and WinDbg, dynamically resolved kernel offsets, built our own user-mode and kernel-mode toolkits, hid drivers and processes, and even tunneled C2 traffic through trusted APIs (like Slack) to evade network-level detection.
But personally, what I REALLY liked about the course is the kernel-level part. It was really the most thorough course I’ve seen on the subject by going into the actual internals of how the Windows kernel and EDR drivers communicate, and showing how to abuse that to neutralize the EDR from below.
Course practice Lab
As for the provided course lab, I really liked how stable it was (it was really that stable during every course I have taken with Altered Security). Every issue I thought I had with the lab turned out to be a skill issue on my side haha. I would also like to really thank the support team, they are REALLY available 24/7, the latest they have ever answered me was after 45mn (They usually respond withing 15mn max). They are really helpful, respectful, patient and know what they’re doing.
I didn’t encounter any issues, latency or lag whatsoever (just make sure to choose the closest location to you geographically when choosing your server access). The lab machines are updated Server 2025 with live EDR running, which is exactly what you want to practice against before the exam.
Exam Environment
The exam is a 48-hour completely hands-on experience on a fully-patched Windows Server 2025 environment with live EDR detection (MDE, Sysmon and Elastic EDR all running together).
You can reboot your exam machine that you’re using or the lab environment.
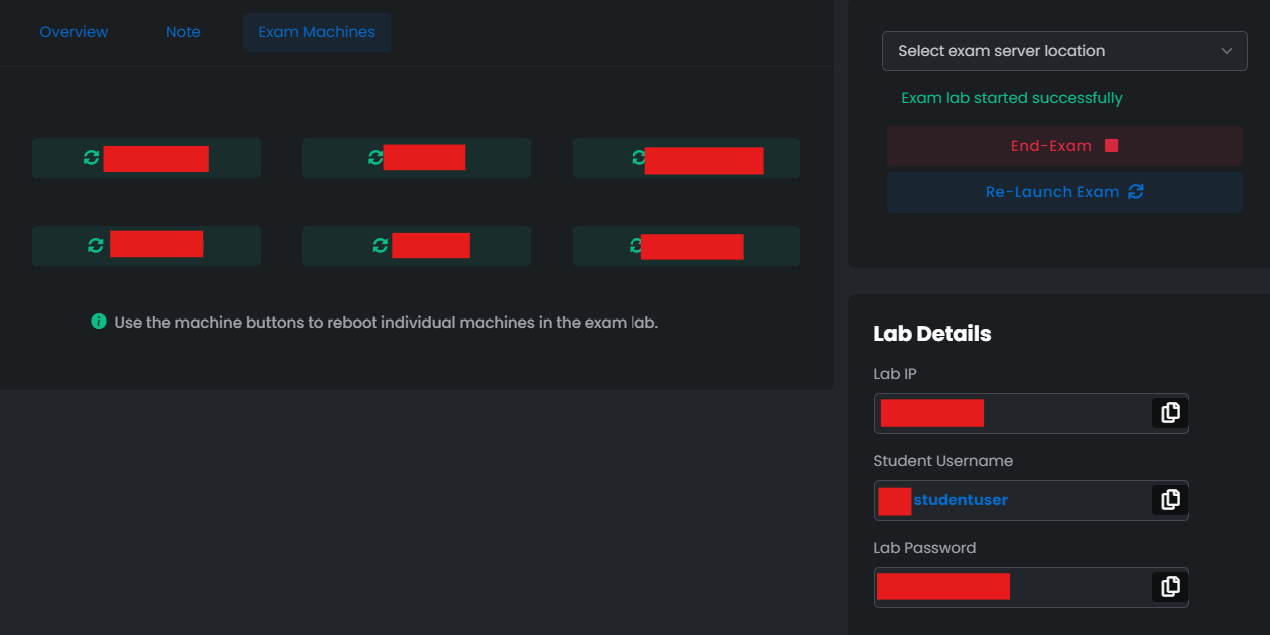
The goal of the exam lab is to complete a series of hands-on practical challenges that test you on the techniques covered in the course: bypassing static detection, neutralizing EDR components, evading telemetry, exploiting vulnerable drivers and demonstrating that you can actually operate stealthily under modern endpoint protection.
A detailed report of the engagement must be delivered withing 48h of the exam attempt ending (which is a very good time to allow you to get some rest). As for me, after my previous experiences with CRTP, CRTE and CARTP I figured to just start writing the report in parallel while attempting the exam: that allowed me to stay organized and not miss any details. (I’m also a bit lazy to write it without lab access later haha)
I managed to complete all the challenges and finish the report well before the deadline. Note that during that time I took breaks, had lunch and dinner, prayed my 5 prayers (priorities of course). So the time was not fully for the exam only. (And I also play Hack The Box machine and make writeups for them weekly that’s why I’m a bit familiar with Windows internals, don’t feel discouraged if it took you more time to achieve it!)
Time Management
One thing that those who think of passing the CETP exam should give a really good thought to, is time management. Since you have 48 hours to complete the challenges and make screenshots of the steps you have taken.
One thing I could advise you to do, is to try and avoid rabbit holes (there isn’t any but still) and don’t get too stuck on a single technique or detection (or something you might think is being detected when it actually isn’t), everything on the course material will be on the exam lab and you don’t have to look for any techniques that you did not study for.
Another tip: have your custom tooling pre-built and tested in the course lab BEFORE you start the exam. Compiling, signing and debugging a kernel driver under exam pressure is really not the move. Treat the exam as the moment to deploy what you’ve already built and validated.
CETP exam pros and cons
Pros:
What I really liked about CETP:
- The extensive course material offered and the Tools/source code that are sufficiant for any red teamer / malware developer during their engagement.
- The really stable lab and exam environments.
- The responsive support team who have never failed to provide students with support.
- Saad and Manthan’s methodology and way of explaining really complex internals by making it sound approachable (the kernel programming sections are gold).
- The realistic side about the techniques treated in the course and the exam: you’re going against actual EDRs, not some toy AV.
- The deep-dive we did on EDR internals, kernel callbacks, ETW and PP/PPL bypass.
- Lifetime access to all the source code and tools, which you can keep building on for your real engagements.
Cons:
- The price point of the lab is a bit higher compared to other Altered Security certs (449$ for 30 days vs 299$ for CRTE), but honestly given the amount of content, the live EDRs in the lab and the depth of the material, it is still reasonable.
- I would have loved to see even more EDR vendors covered in the exam lab (like SentinelOne or CrowdStrike), but having MDE + Sysmon + Elastic running simultaneously is already a really solid challenge.
Things I’d like to see in the future
The course already covers MDE, Sysmon and Elastic EDR which is great, but seeing a future module or lab extension covering other widely-deployed solutions like SentinelOne, CrowdStrike Falcon or Cortex XDR would really step up the game. These vendors have very different telemetry and detection logic, so practicing against them would make the certification even more aligned with what red teamers actually face on real engagements.
Also, an additional module on more advanced initial access tradecraft (beyond signed ClickOnce backdooring) would be a really nice addition, since modern phishing payloads and loader development is a whole field on its own.
Practical Tips
Some tips that will help you alond the way:
- Take notes, they will REALLY help you while studying and you can get back to them anytime. For CETP especially, structure your notes by EDR component (telemetry source, kernel callback, ETW provider, etc.) so you know exactly which technique kills which detection.
- Build, compile and TEST your tooling in the course lab. Don’t trust a tool you haven’t run yourself.
- If you feel too stuck, try restarting the machines. Errors may occur, especially with kernel-level stuff (BSODs are part of the journey haha).
- Remember to get some sleep or to take a 10mn walk if you feel stuck, it can really refresh your mind. Kernel debugging at 3am with no sleep is rarely productive.
- Review your course notes and lab notes before passing the exam, also keep them open on the side for easy access.
- Get comfortable with IDA Pro and WinDbg before the exam, you’ll really need them.
- Always try to think out of the box and as a creator of the exam, it’ll give you new insights.
- Stay hydrated :=) (seriously haha)
Personal Opinion
I really loved the CETP exam. Great course material, responsive lab support team, stable infrastructure both for the course and exam lab, and honestly some of the most technical content I’ve gone through in a certification. It is a great Certification for anyone looking to get into modern EDR evasion, malware development or advanced red team tradecraft.
The CETP really fills a gap in the certification space: most red team certs stop at “you got Domain Admin”, but CETP starts where the real challenge begins, which is actually staying undetected against modern endpoint protection. Big shoutout to Saad and Manthan for putting together such a deep and well-crafted course.
I will hopefully be getting back for CRTM/CARTE (expert and master) certifications, also from Altered Security.
Stay tuned ! Hope you enjoyed this blog post, and see you soon with a new review!
- Foued SAIDI (A.K.A. 0xkujen)
- Title: Certified Evasion Techniques Professional (CETP) - Review 🚀
- Author: Foued SAIDI
- Created at : 2026-04-25 10:16:46
- Updated at : 2026-04-25 13:08:13
- Link: https://kujen5.github.io/2026/04/25/Certified-Evasion-Techniques-Professional-CETP-Review-🚀/
- License: This work is licensed under CC BY-NC-SA 4.0.