International Cybersecurity Challenge (ICC) - Tokyo, Japan

Overview

In this blog post, I will be sharing my personal experience as a first-time participant of the International CyberSecurity Challenge (ICC) during its’ fourth (4th) edition representing the Africa Regional Cybersecurity Committee (AFRICC) competing against the top qualified players from 8 regions covering the whole globe.
Whoami
This is Foued SAIDI (a.k.a. 0xkujen), I work as a Senior Penetration Tester within Intrinsic-Security at Doha, Qatar.
I am a very active CTF player with my team PwnSec.
I am also aspiring to become the best Web3/Blockchain Security Researcher out there!
I have had some cool international CTF experiences across my very short career:
- Kaspersky Security Analyst Summit (SAS) Conference in Khao Lak, Thailand. You can read more about it in this blog post.
- Cyber Security Awareness Week (CSAW) Jeopardy-Style CTF Finals (2023) [Top 8] and Hack My Robot (2024) [2nd Place] organized by New York University Abu Dhabi (NYUAD) in Abu Dhabi, UAE.
- GITEX Global Finals CTF [Top 10] in Dubai, UAE.
- GISEC Global Cyber Drill (138 countries, 11 Guinness World Records) [Top 7 and Top 4 representing Tunisia] in Dubai, UAE.
- Hack The Box Business CTF 2025 (including Microsoft, Cisco, Paypal, Synacktiv,…) [7th place / 796].
And a lot other participations both locally and internationally.
I am also:
- Hack The Box Elite Hacker [best: Top 60 WorldWide and Top 1 on Tunisia]
- Technical Manager for SecuriNets -first cyber security association in Tunisia- for 2 years, authored and organized 15+ CTFs, performed 50+ workshops and conference talks.
- CRTP, CRTE, CADPenXv2 and CARTP certified. Currently preparing for CETP.
International CyberSecurity Challenge (ICC) Overview

The International Cybersecurity Challenge is a cybersecurity competition created and organised by a global consortium including Europe (European Union Agency for Cybersecurity (ENISA) ), Asia (Code Blue, Div0, BoB, Bitscore), USA (Katzcy), Canada (Cyber*Sci), Oceania (The University of Queensland ), Africa (Namibia University of Science and Technology ), and Latin America (ICC Latino America).
The participants, all aged 26 or younger, compete in eight teams that have advanced through representatives.
The competition features both Jeopardy and Attack-and-Defense challenges.
The way I see it, you can look at the ICC as the World Cup of CyberSecurity (it really is haha). It gathers teams from the whole globe, after passing qualification stages with their own countries and eventually gather on team to represent their continent is a WorldWide clash.
History
The International CyberSecurity Challenge (ICC) has witnessed its’ first edition in 2021 where the event was held Athens, Greece between 14 and 17 June where team Europe claimed the first place, team Asia second and team USA third.
The second edition was held in San Diego, California between 1 and 4 August where team Europe once again claimed the win back-to-back, team Oceania coming up second and team Asia settling for third place.
And the third edition was held in Santiago, Chile from 28th October to 1st November where team Europe had a back-to-back-to-back win streak, as where the second and third ranks were claimed by team Asia and team Oceania.
AFRICC team
African Region to Cybersecurity Competition (AFRICC) was established in 2021 to develop original african talent in order to create a team that will represent the continent in the International Cyber Security Challenge.
The AFRICC team was pretty diversified this year gathering players from 10+ african countries (Tunisia, Morocco, Namibia, Uganda, Nigeria, South Africa, Zimbabwe, etc.).
This was unfortunately our first appearance onsite for the ICC finals, since the team has 17 members which makes getting sponsorship a bit challenging.
AFRICC qualification
In order for players to be eligible to participate in the ICC, they have to through qualifier rounds within their continent. An example of this is the Europe CyberSecurity Challenge that facilitates the qualification process for team Europe.
However, since Africa did not really have a qualification competition, the choosing on players was based off on some other criterias:
- Players performance throughout the year.
- Willingness to participate and represent team AFRICC in the ICC. (passion)
- Individual skill.
- Specialties when it comes to Security and CTF categories.
- Team play and being a good and positive team player.
- Multiple particiations in CTFs throughout the year which will help in allowing the player to gain more knowledge.
Finals Preparations
The team needed to do some preparation in order to be fully ready for the finals. For this we extend our thanks to the Organizing committee of the tokyo ICC since they provided us with two dry runs for preparations purposes. It had basically two objectives:
- Familiarize players with the challenges, platform, submission, infrastructure.
- Test the platform and system for bugs or vulnerabilities.
To be honest, only 2 2-hour dry runs were not enough. This comes back to the reason that the ICC infrastructure for 2025 was very different from other Attack-Defense CTFs for example (more on this later in the post.). So I personally spent more time trying to figure out how to deal with the system instead of developing more tools, etc.
But it was great overall. Also, team AFRICC got 1st place in the second dry run which was very good for the morale of the team: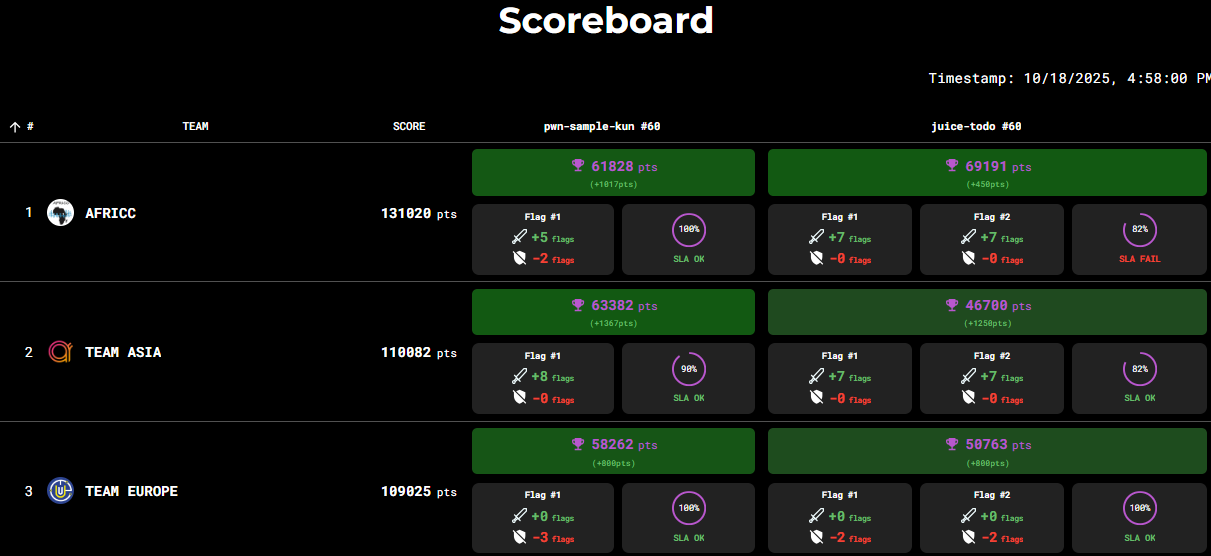
Atmosphere of oversees participation


The International CyberSecurity Challenge (ICC) was held in Tokyo, Japan. More specifically in New Otani Makuhari Hotel (which was an amazing venue).
This was my very first time every travelling to Japan, the process was so smooth at the airport as it has some state-of-the-art machinery to ease the entry process for foreigners. Even tho I was questioned for 20mn because I put Tourism instead of Conference in the Travel reason 😭
Anyways, I liked it 👌
International CyberSecurity Challenge event
The ICC ran for a total of 5 days:
Day 0 - Setup
Unfortunately I only joined on the second day because I was working on the first day of the ICC. I took the plane 1AM Doha time and reached Tokyo by 8PM. It was a pretty long flight with a 2h transit over China airport through China Southern Airlines . To be frank, CSR were not up to my expectations since they did not provide a Halal/vegetarian meal on the plane so i ended up not eating almost anything because I am muslim. I hope they change this in the future!!
Day 1 - Warmup
This one was pretty funny, because I jet lag and my lack of focus, I thought that the second day was actually the competition day 😂
It turned out to be the opening ceremony + warmup day.
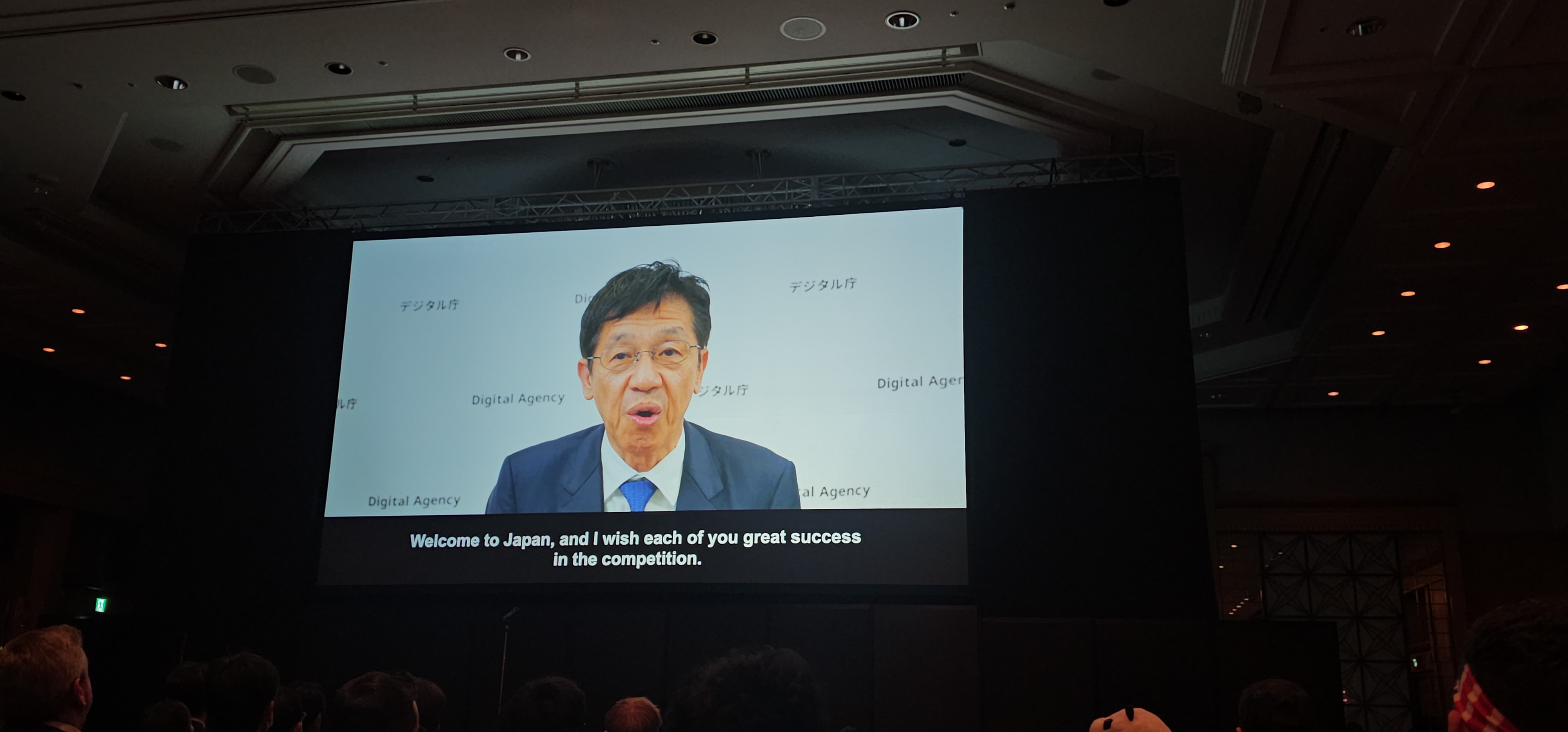
At first, the Japanese Minister of Cyber Security gave us an opening word:
Also check out our super cool AFRICC team poster made by the organizers:

Later, the organizer opened both the Jeopardy and the Attack-Defense networks for testing purposes by the players. It was a pretty good decision since there were some minor network issues that were resolved later.
Off to day 2!
Day 2 - Jeopardy CTF
A Jeopardy-Style Capture the Flag (CTF) competition is a cybersecurity challenge that provides players with standalone challenges that are not linked and that revolves around the following categories:
- Web Exploitation
- Reverse Engineering
- Binary Exploitation
- Digital Forensics and Incident Response
- Cryptography
- Cloud
- AI/LLM hacking
- Blockchain/Web3
- FullPwn (pentesting)
- Hardware hacking
The CTF span across 9 hours and almost 6 categories. It was pretty intense as the coordination that had to be done was crazy since we were 15 players on the team, hard and numerous challenges, scoreboard pressure, etc.
I am pleased that we got 7th place in the Jeopardy CTF, after countless hours and trial and error. I especially worked on a Windows Blue Team challenge where you had to fix 3 vulnerabilities to get the flag. That challenge was only solved by team Oceania and I had a huge skill issue where I forgot that the krbtgt account password had to be rotated a couple of times and I did not check the last time it was set 😭 But learned a lot from it!

Day 3 - Attack-Defense CTF
You can read in detail what an Attack/Defense CTF is from this previous Kaspersky SAS Conference blog post.
This Attack/Defense was especially very very special and different from what you would typically see in an A/D CTF.
First of all, the authors were some of the best WorldWide.
Second, during the ICC, you are not provided with direct access to the vulnbox which will be holding your services/infra. So how did it work? Let me tell you:
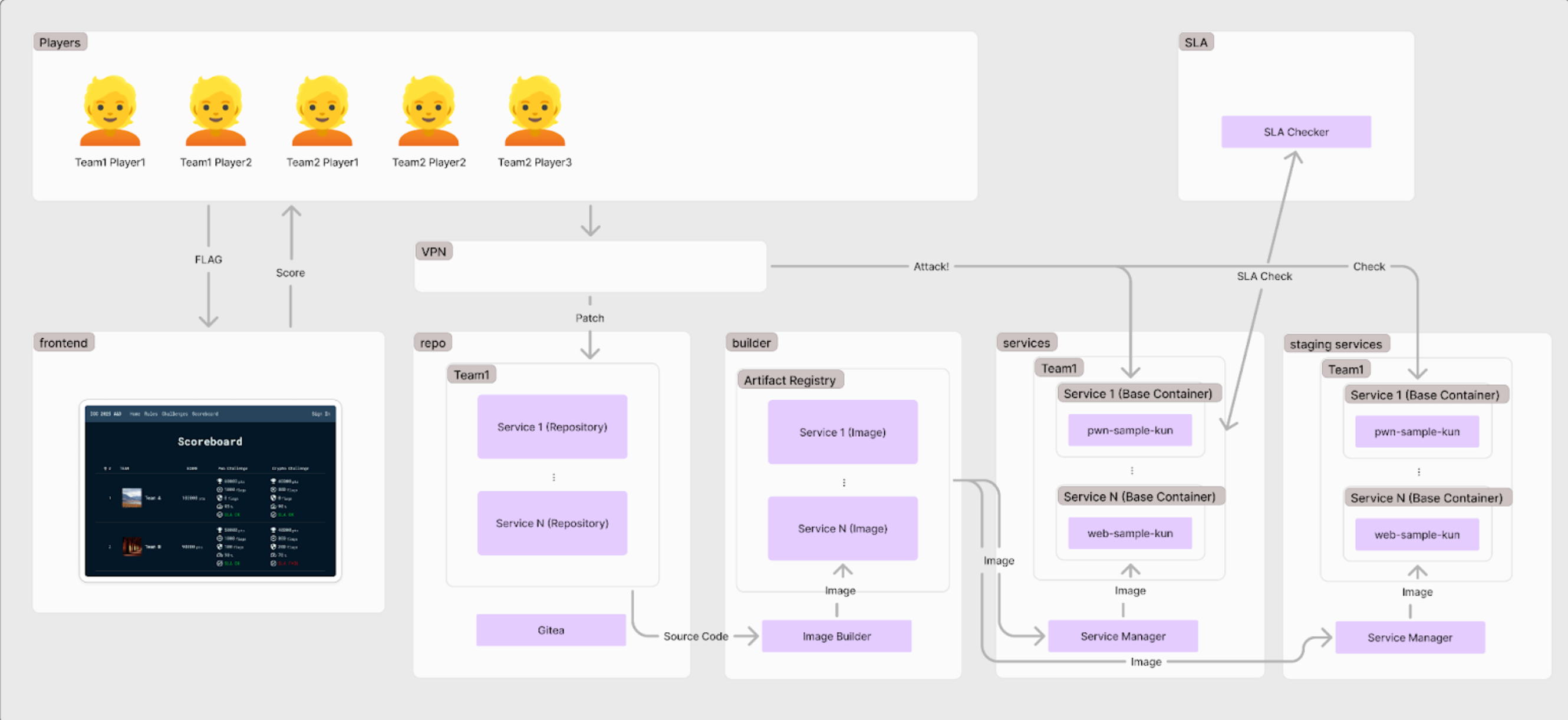
For this infra, here is what you have access to:
- A team token that allows you to connect to the platform where you have access to the following:
- A Gitea instance which has a staging and a production environment (In this case, they are the same. However they were not during the dry run). You can push your patches to the staging envrionment first to check if your patches work fine. Then you can push them to the production. But in this case it was the same push which was a bit bad.
- A tab containing PCAP files (network dumps) of the traffic that is incoming to your services. This excludes the traffic incoming from the checker system (admin) so players don’t replicate the ongoing checks.
- A tab containing Build Histories for your commits and if they were built successfully.
- A tab containing SLA Histories detailing if your build match the SLA or break it.
- A tab containing the IP addresses for your your services under this format:
10.3.<team_id>.1:8080(for example). This way your also know your opponents IP address for their services.
- As for patching, after cloning the github repo for the code, you will get a
/patchabledirectory containing either a config file where you will insert firewall rules or update the source code itself to patch vulnerabilities. Of course all of this is while maintaining a valid SLA.
So you can tell from this that the infra was not something you would typically see in an Attack/Defense CTF and that it was a bit confusing at first. That is why dry runs were put in place.
Unfortunately we ended up with a not so good position for the Attack/Defense CTF, simply because the players we were playing against had far more experience and tooling than our team. But this is only a motive to keep pushing forward and to win it next year Inshalah!!
This A/D set was very thrilling because you had to :
- Focus on source code review and analysis.
- Focus on patching the source code and on configuring firewalls.
- Focus on PCAP files analysis (which come 8 rounds later to not steal flags real time) for exploit development.
- Focus on keeping your patches fully working so SLA does not drop.
- Focus on automating both the offensive and the defensive strategies.
The pressure was high up in the sky as you had to balance doing all of these steps, it was amazing!
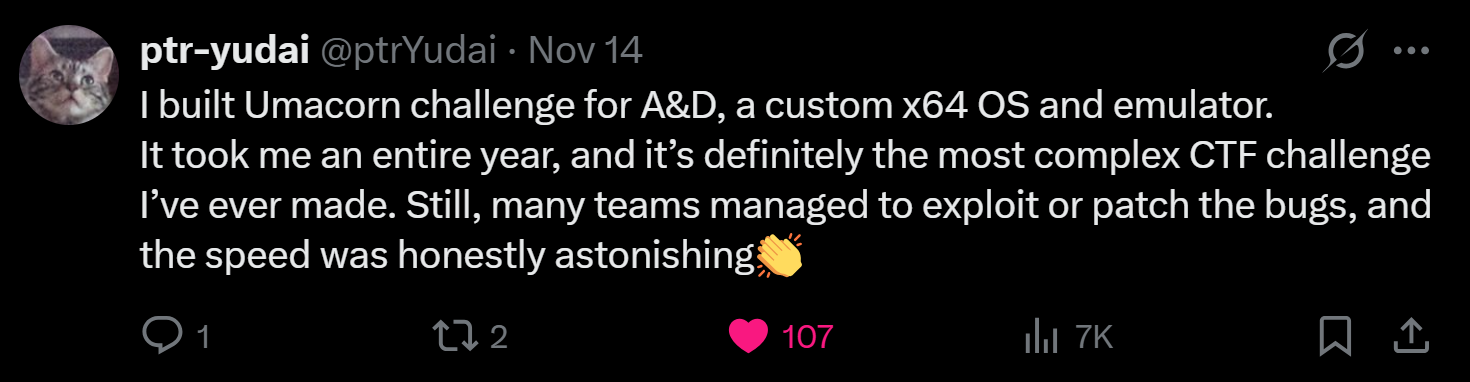
As for the services, we had some really cool and realistic services. One very interesting service (which I unfortunately did not solve) was Umacorn: a custom x64 OS and emulator built on a whole other CPU architecture. It was built by the GOAT @ptr-yudai who spent a WHOLE YEAR developing the challenge and had intentionally the following vulnerabilities:
- negative fd allowed
- rng seed can be any address
- file password address can point to disk cache (eg comparing password to itself)
- fwrite allowed arb write to kernel memory
- no memzero for freed pages -> realloc to get flag
- pagealloc error -> return value is assumed to be valid address nontheless (get physical page 0)
- table UAF
- fopen name could be flag1
- kernel memory was rw initially
- write syscall can read arb memory
- most password compares could be timeable
- strcpy in fopen
- kernel uses movs instruction but doesn’t call cld so you could call std in userland and cause stack overflow in kernel
This was crazy to be honest!

Day 4 - Awards ceremony and Departure day
Unfortunately my plane was at 15h40 so I had to go early to the airport which resulted in me missing the award ceremony, however they provided us with coins (kindof medals) as a token of appreciation for our participation:


Later that day, I was lucky to get a Windows seat to witness the magical Japanese clouds, mountains and sunset:



Takeaways & Lessons learned
The ICC was one the best I have attended in my life, and what made it even more magical was going to Japan for the first time.
From the amazing competition, to competing against the best, to connecting with like-minded people and touch some grass (and clouds!).
What did I learn from all of this?
- Automation is key both on the offensive and defensive.
- Time management is brutal, if you waste time at stuff and don’t talk it over before the event you will be truly lost.
- The coordination that has to be done between attacking and defending/patching is crazy.
However, the most important thing I feel I learned here and that I keep feeling and igniting each time is:
- If you want to become the best, you have face the best, be on the same stages as them, talk and learn from them and eventually you will beat them!
No one came to the finals overnight, continents have made qualifiers choosing from over hundreds of players worldwide. So it is truly the best of the best.
Being there not only motivated me to go back and win the ICC with AFRICC next year, but to also get better at what I am doing. There is no time to stay behind or lose progress.
And that is exactly why I love going to events: it will make me want to become better, push harder, go beyond my limits as nothing holds me back. Anything is possible with a true faith and trust in Allah SWT
After each event, I go back home dreaming of getting my first 0-day, CVE, winning at pwn2own, and much more haha. And I truly believe I will get there one day Inshalah.
=> If you believe it, truly believe it and work as hard as you can for it, you can get it and become the best at it.
It is also very important in my opinion to keep going to such events at a young age and profiting to the max, since responsibilities increase with age.
Future Events
I do not believe I will have any more onsite events from now until the end of 2025. Only online competitions.
But for next year Inshalah? I am working on becoming the best and winning it all:
- Kaspersky SAS Con
- ICC
- Blackhat MEA
- CSAW
- GITEX
- GISEC
If a person works hard enough, they can do the impossible.
Conclusion
The International CyberSecurity Challenge was one of the best events that I have ever attended in my life. I will keep going to it each year and eventually Inshalah become a coach for the AFRICC team.
It is very important to try and stay as motivated and as updated as possible in Cyber Security.
Always stay humble, always remember where you came from, always work as hard as you can, and you will get there!
Adios!
-Foued SAIDI
- Title: International Cybersecurity Challenge (ICC) - Tokyo, Japan
- Author: Foued SAIDI
- Created at : 2025-11-21 21:37:50
- Updated at : 2025-11-21 21:42:08
- Link: https://kujen5.github.io/2025/11/21/International-Cybersecurity-Challenge-ICC-Tokyo-Japan/
- License: This work is licensed under CC BY-NC-SA 4.0.